Developers are issuing hotfix

Brave, the privacy-focused web browser, is exposing users’ activity on Tor’s hidden servers – aka the ‘dark web’ – to their internet service providers, it has been confirmed.
Brave is shipped with a built-in feature that integrates the Tor anonymity network into the browser, providing both security and privacy features that can help obscure a user’s activity on the web.
Tor is also used to access .onion websites, which are hosted on the dark net.
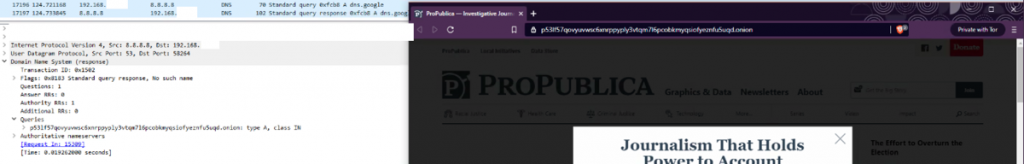
DNS requests are unencrypted, meaning that any requests to access .onion sites using the Tor feature in Brave can be tracked – a direct contradiction to its purpose in the first place.
The blog post reads: “Your ISP or DNS provider will know that a request made to a specific Tor site was made by your IP. With Brave, your ISP would know that you accessed somesketchyonionsite.onion.”
Following the disclosure, well-known security researchers including PortSwigger Web Security’s James Kettle independently verified the issue using the Wireshark packet analysis tool.
“I just confirmed that yes, Brave browsers Tor mode appear to leak all the .onion addresses you visit to your DNS provider,” Kettle tweeted, providing a screenshot for evidence.